🔗 View in your browser. | ✍️ Publish on FAUN.dev | 🦄 Become a sponsor
KubernetesLinks
This Week in Kubernetes, with Kaptain the Shark
📝 A Few Words
Quick heads-up on CVE-2026-42880 (Argo CD).
What it is: a read-only user can extract plaintext Kubernetes Secrets through the ServerSideDiff endpoint. CVSS 9.6. Disclosed May 7, 2026 by researcher Hoang-Prod.
How it works: the endpoint relies on a defense layer called removeWebhookMutation to strip sensitive fields from Server-Side Apply dry-run responses. That defense is skipped when an application has the annotation argocd.argoproj.io/compare-options: IncludeMutationWebhook=true. With the annotation set, the dry-run returns raw etcd data, including service account tokens, database credentials, API keys, and TLS certs.
Who is affected: Argo CD 3.2.0 to 3.2.10 and 3.3.0 to 3.3.8, AND at least one application using the IncludeMutationWebhook annotation. A PoC Python script already exists.
Fix: upgrade to 3.2.11 or 3.3.9.
If you cannot upgrade today: audit your applications for the IncludeMutationWebhook annotation and remove it from any application that does not strictly need it.
Have a great week,
Aymen
What it is: a read-only user can extract plaintext Kubernetes Secrets through the ServerSideDiff endpoint. CVSS 9.6. Disclosed May 7, 2026 by researcher Hoang-Prod.
How it works: the endpoint relies on a defense layer called removeWebhookMutation to strip sensitive fields from Server-Side Apply dry-run responses. That defense is skipped when an application has the annotation argocd.argoproj.io/compare-options: IncludeMutationWebhook=true. With the annotation set, the dry-run returns raw etcd data, including service account tokens, database credentials, API keys, and TLS certs.
Who is affected: Argo CD 3.2.0 to 3.2.10 and 3.3.0 to 3.3.8, AND at least one application using the IncludeMutationWebhook annotation. A PoC Python script already exists.
Fix: upgrade to 3.2.11 or 3.3.9.
If you cannot upgrade today: audit your applications for the IncludeMutationWebhook annotation and remove it from any application that does not strictly need it.
Have a great week,
Aymen

🔍 Inside this Issue
Kubernetes v1.36 is quietly rewriting the rules: less handwritten Go, more declarative guardrails, and controllers that stop tripping over each other at scale. Pair that with a real-world supply chain hit on a CNCF project, and the throughline is clear: your cluster is only as safe and efficient as the boring details.
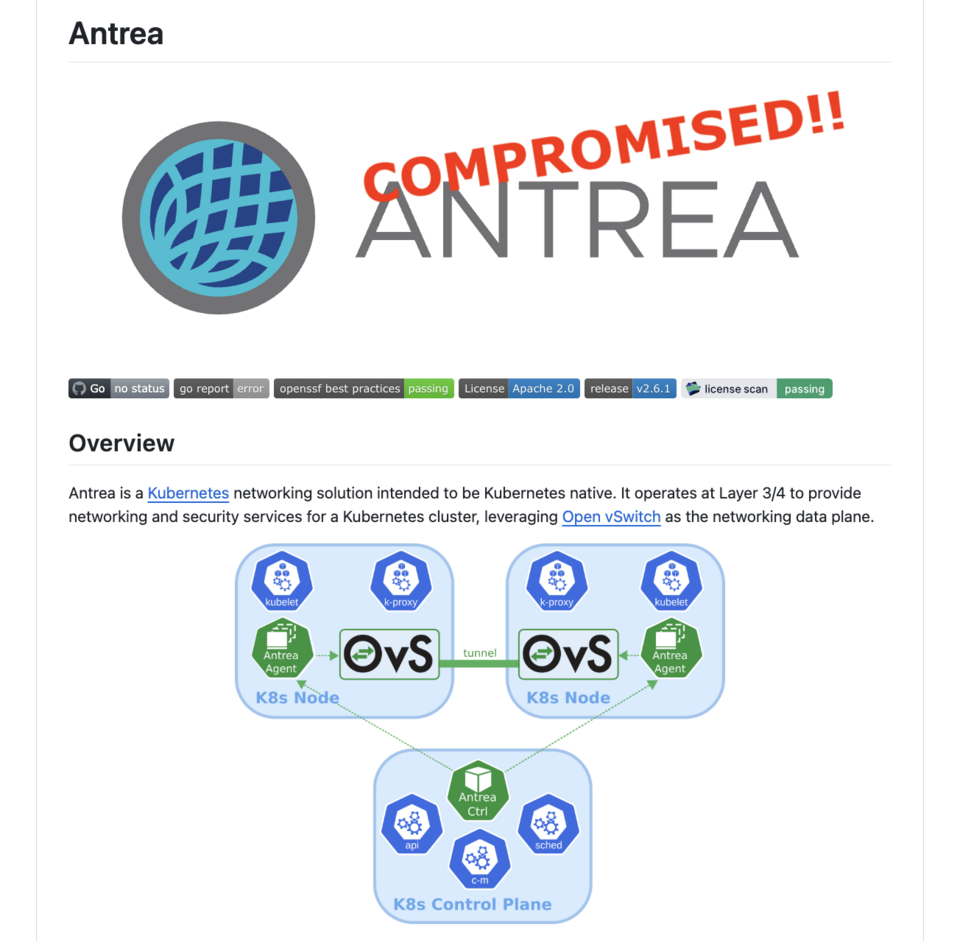
🚨 CNCF Project Antrea Compromised in Daring GitHub Attack
✅ v1.36: Declarative Validation Graduates to GA
📸 v1.36: Moving Volume Group Snapshots to GA
🧩 v1.36: Server-Side Sharded List and Watch
Go tighten the screws before the next incident (or scale test) does it for you.
Happy coding!
FAUN.dev() Team
🚨 CNCF Project Antrea Compromised in Daring GitHub Attack
✅ v1.36: Declarative Validation Graduates to GA
📸 v1.36: Moving Volume Group Snapshots to GA
🧩 v1.36: Server-Side Sharded List and Watch
Go tighten the screws before the next incident (or scale test) does it for you.
Happy coding!
FAUN.dev() Team
⭐ Patrons
iacconf.com
Your team can prompt its way to “working” Terraform. The problem is everything the model cannot see. In the IaCConf Keynote, Corey Quinn from Duckbill will break down failure modes, hidden dependencies, and why “it compiles” is a dangerous bar. You’ll walk away with a framework to review and constrain AI-generated IaC safely.
May 14. Free to attend. Register now.
May 14. Free to attend. Register now.
eventbrite.co.uk
Modern platform teams are under pressure to scale cloud-native systems faster while improving reliability, security, developer experience, and operational efficiency. AI is changing how platforms are designed and operated — from intelligent automation and observability to AI-native developer platforms and autonomous operations.
Join leading experts from WSO2, CNCF, cloud-native, and DevSecOps communities for a practical workshop focused on building scalable, secure, and intelligent AI-native platforms.
Register Here: Building AI-Native Platform Engineering Systems Tickets, Saturday, May 30 • 7 PM - 11:59 PM GMT+5 | Eventbrite
Join leading experts from WSO2, CNCF, cloud-native, and DevSecOps communities for a practical workshop focused on building scalable, secure, and intelligent AI-native platforms.
Register Here: Building AI-Native Platform Engineering Systems Tickets, Saturday, May 30 • 7 PM - 11:59 PM GMT+5 | Eventbrite
⭐ Sponsors
eventbrite.co.uk
Are Your APIs Ready for AI Agents? A Hands-on Workshop on May 23rd
AI agents are beginning to autonomously call APIs, chain services, and create integrations that most platforms were never designed to handle. This hands-on masterclass on Designing AI-ready APIs helps architects and developers build governed, predictable API ecosystems using OpenAPI, Overlay, and Arazzo.
Learn how to add guardrails, improve discoverability, and safely evolve existing APIs for automated consumption.
FAUN.dev readers get an exclusive 40% discount using code FAUN40.
AI agents are beginning to autonomously call APIs, chain services, and create integrations that most platforms were never designed to handle. This hands-on masterclass on Designing AI-ready APIs helps architects and developers build governed, predictable API ecosystems using OpenAPI, Overlay, and Arazzo.
Learn how to add guardrails, improve discoverability, and safely evolve existing APIs for automated consumption.
FAUN.dev readers get an exclusive 40% discount using code FAUN40.
bytevibe.co
kubectl get pods.
kubectl logs.
kubectl describe.
kubectl apply.
kubectl exec.
You typed it 3,413 times this week. Wear it!
Code FAUNDEV10 for 10% off.
kubectl logs.
kubectl describe.
kubectl apply.
kubectl exec.
You typed it 3,413 times this week. Wear it!
Code FAUNDEV10 for 10% off.
🔗 Stories, Tutorials & Articles
kubernetes.io
Alpha in v1.36, server-side sharded list and watch adds a shardSelector field to ListOptions so the API server uses an FNV-1a hash on metadata.uid or metadata.namespace to send each controller replica only its slice of the resource collection. This eliminates the cost of every replica deserializing the full event stream just to discard objects it does not own.
kubernetes.io
Declarative validation graduated to GA in Kubernetes v1.36, replacing handwritten Go validation with +k8s: marker tags on field definitions.
kubernetes.io
Volume group snapshots reached GA in Kubernetes v1.36, with the API promoted to groupsnapshot.storage.k8s.io/v1. The feature lets a VolumeGroupSnapshot object take crash-consistent snapshots across multiple PVCs selected by label, removing the need to quiesce applications that span separate data and log volumes.
mirantis.com
A vendor piece from Mirantis arguing that GPU multi-tenancy on Kubernetes is widely misrepresented, with most platforms shipping namespace-based isolation while production GPU clouds require hardware-enforced separation through MIG partitioning, cluster-per-tenant architecture, and DPU-based network isolation. The post positions Mirantis's open source k0rdent as the composable answer, claiming a 15-to-20-minute path from cluster provisioning to a running AI workload.
opensourcemalware.com
A throwaway GitHub account compromised CNCF project Antrea's Jenkins infrastructure on May 2 by opening a malicious PR and firing /test-* slash-commands that detonated the workflow against PR-fork code with credentials in scope. The same operator ran parallel campaigns against at least seven other projects that week.
⚙️ Tools, Apps & Software
github.com
A read-only WebUI dashboard for Kubernetes cluster monitoring. Designed for end-users unfamiliar with Kubernetes and for cluster admins who want a quick status overview. Also exposes a fully functional REST API for integration with other tools.
github.com
34 FinOps specialist AI agents + 6 named-pattern playbooks. Drop into Claude Code, Copilot, Cursor, Windsurf, Aider, Gemini CLI. MIT.
github.com
Modern Kubernetes visibility. Topology, event timeline, and service traffic — plus resource browsing and Helm management.
🤔 Did you know?
Did you know that NetworkPolicies in Kubernetes only work if your cluster runs a network plugin that knows how to enforce them, and even then the rules can interact in surprising ways with how Services route traffic? Kubernetes itself does not implement NetworkPolicy. That job is delegated to your CNI plugin (the component that wires up pod networking), such as Calico or Cilium. The official docs warn that when packets get their addresses rewritten on the way through a Service, it is not strictly defined whether that happens before or after policy checks, which is one reason projects like Cilium move both service routing and policy enforcement into the kernel using eBPF so the order is predictable.
🤖 Once, SenseiOne Said
"Kubernetes makes every service easy to deploy and hard to understand. The container boundary cleans up your machine and dirties your failure modes. If you cannot explain what happens when etcd is slow, you do not have a platform, you have a rumor."
SenseiOne
SenseiOne
⚡Growth Notes
Two engineers hit the same latency spike after a deploy. One adds a retry with exponential backoff on the failing call and ships a fix by lunch; the other traces the call graph, finds three services synchronously waiting on the same downstream, and spends the week turning two of those calls into events.
😂 Meme of the week